Synopsis:
“Cybersecurity in 2024 is all about prioritizing defense dollar spending and having a security framework that provides threat intelligence, enabling robust cybersecurity strategies and apparatus.” Nehal Shah, the Solution Architect at Sigma Solve, explains the grave cyber security scenarios that are prevailing in our digital world today.
There are relentless security challenges and out-of-the-box solutions, too. As a cybersecurity solution provider, we aim to empower you with a comprehensive understanding of the cybersecurity sphere, its implications for businesses, and ways to mitigate these threats concurrently through this blog.
Conquer Cybersecurity Challenges in 2024 and Beyond:
Today, cybersecurity has taken precedence over performance. For businesses, cybersecurity solution architecture is as essential as performance-driven growth. Cybersecurity is all about protecting digital assets from unauthorized access, cyberattacks, and data breaches, which is of paramount importance.
Cybersecurity is pivotal in safeguarding critical information to prevent financial losses, avoid legal consequences, manage reputation, ensure business continuity, and preserve customer trust. Therefore, developing a robust security strategy must entail multi-factor authentication, insider threat detection, supply chain security, data loss prevention, and zero trust architecture, among other measures.

A Glimpse into Today’s Top Cybersecurity Threats:
The growth in cybersecurity threats is proportional to the growth of technological innovation. As technology advances, there are bad tech guys who want to misuse it for money or pleasure. Cybersecurity solution providers often suggest staying in sync with emerging cybersecurity threats today.
Ransomware Attacks: These attacks involve malware that breaches basic system security, ciphers data, and seeks ransom money from victims to restore their access. Such attacks on massive organizations have increased recently.
Phishing and Social Engineering: Phishing has been the most common way in which attackers trick victims into revealing sensitive financial information and use that information to cause financial damage to victims.
Advanced Persistent Threats (APTs): ATPs are consistent and continuous and don’t stop without disrupting operations or stealing data. Usually, enemy nations carry out such cyber attacks to put a hold on their missions.
IoT Vulnerabilities: IoT devices are usually more prone to cyberattacks, given their low-security levels and open-ended connectivity. It is usually used for data theft or blocking the services that these devices offer.
Supply Chain Attacks: Third-party apps aren’t fully security-proof. Attackers target such TPAs to enter into large organizations, aiming for data theft, stealing financial details, or business secrets, resulting in operational damages.
Zero-Day Exploits: Attackers target enterprise software that lacks security patches or is seldom updated. ZDEs are among the most dangerous attacks, as they render businesses defenseless and breach the entire system.
Cloud Security Threats: Clouds, despite their indisputable security features, are vulnerable to cyber attacks through misconfigurations or unauthorized access. The impenetrable cloud environment is the need of the hour.
AI and ML Attacks: Attackers can breach AI-powered applications and cause infrastructural damage or biased responses, or they can alter the ML algorithms to manipulate the inputs to damage automated workflows or data.
Why Cybersecurity Isn’t an Option, It’s a Necessity:
If you can leave your home unlocked, you can leave your business undefended. Although the offense is not the ideal defense in the realm of cybersecurity, there is no alternative to IT security services and an impenetrable security apparatus that protects not only the data but also the applications, networks, and infrastructure.
Today, businesses must adapt to behavioral analytics, dark web monitoring, quantum cryptography, and extended detection and response (XDR), among other cybersecurity measures, to prevent businesses from financial losses and reputational damages. Let’s understand the impact of cyberattacks on businesses.
Financial Losses: Desaster recovery costs or ransom costs are exponentially high, which may impact the ROI due to operational stagnation. It may also invite penalties from authorities for personal data theft.
Operational Disruption: If data is lost, business processes are affected. If the system is breached, operations experience downtime. Supply chain attacks may cripple the entire business activities for a long time, causing massive damage.
Reputational Damage: Trust is vital for business success. Cyberattacks are often carried out to cause reputational damage that may erode customer confidence, cripple financial systems, and damage brand position.
Legal Consequences: In addition to financial penalties, regulatory authorities may restrict benefits or market access. Businesses may become involved in legal battles over compensation to victims.
Strategic Impediment: Businesses may lose the rights to products and be severely hampered in their capabilities to innovate and grow. Moreover, operational and security costs may continue to rise, affecting profitability.
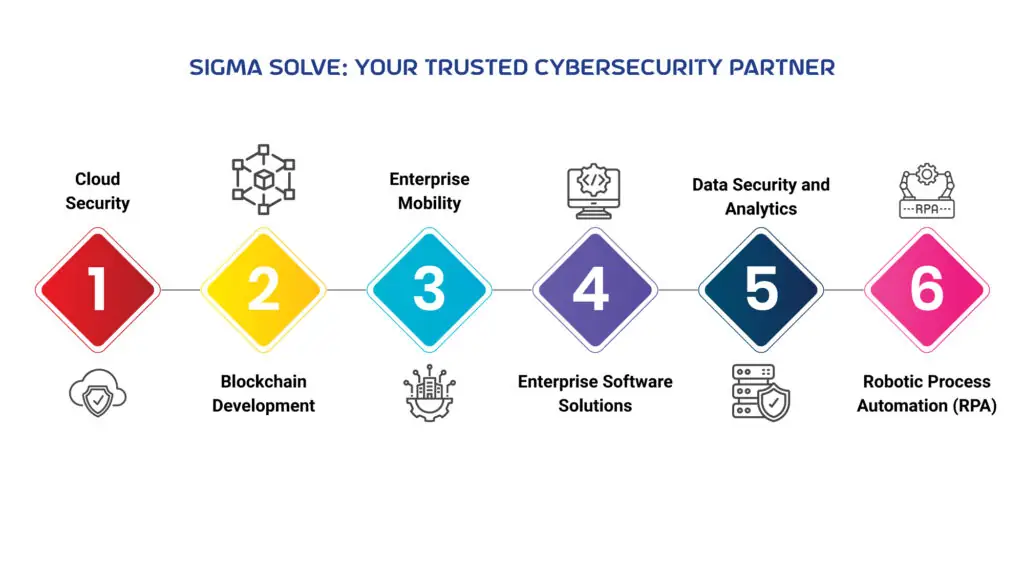
Sigma Solve: Your Trusted Cybersecurity Partner:
As digital transformation is narrowing even the virtual distance and emerging technologies are competing with humans’ cognitive capabilities, preserving the essence and securing digital assets has become the top priority for businesses across the globe.
Above and beyond growth strategies, businesses are advised by the Cybersecurity solution providers to be ready to prevent, detect, respond, and recover from cybersecurity attacks. With advanced cybersecurity innovations and tailored cybersecurity strategies, Sigma Solve delivers a Complete toolkit of strategic cybersecurity solutions entailing blockchain development services, AI-powered cybersecurity solutions, fraud detection solutions, and advanced alert systems, among others, to prevent businesses from falling prey to bad tech guys.
Artificial intelligence:
AI and automation solutions identify threat patterns to detect and respond to cyber threats. Sigma Solve developed AI security solutions to help businesses recognize and mitigate cyber threats.
Cloud Security:
Sigma Solve’s cloud consulting services entail cloud security solutions for cloud migration and cloud applications following the best practices for cloud-native cybersecurity to prevent unauthorized access.
Blockchain Development:
Our blockchain development services include measures that prevent data manipulation and ensure data validation to protect businesses from fraudulent transactions to maintain transparency and security.
Enterprise Mobility:
Sigma Solve protects remote work environments from unauthorized access and mitigates mobile threats to secure communication channels, developing robust enterprise mobility solutions.
Enterprise Software Solutions:
Integrating cybersecurity solutions in application development helps Sigma Solve protect software development, testing, and deployment against SQL injection or cross-site scripting.
Data Security and Analytics:
Data encryption, authorization, validation, and authentication are part of Sigma Solve’s data management solutions. Business intelligence and analytics solutions leverage data analytics for cybersecurity.
Robotic Process Automation (RPA):
Leveraging RPA solutions, Sigma Solve automates business processes to prevent manual entries and human errors, thus improving the efficiency and consistency of security measures.
Your Shield and Sword in the Digital Age:
The digital era demands that businesses protect themselves and mitigate cybersecurity threats to avoid business breakdown. Being your technology partner, Sigma Solve develops advanced cybersecurity solutions that leverage emerging technologies to provide head-to-toe protection.
From advanced detection to preempt resolution to disaster recovery, Sigma Solve ensures that businesses focus on their activities and leave security concerns to them. Call us at +1 954-397-0800 for a consultation to develop a tailored cybersecurity strategy for your digital assets and customer data.
Original Source: https://www.sigmasolve.com/how-sigma-solve-resolves-cybersecurity-challenges/


